Especialistas y Líderes en Ciberseguridad por más de 26 años
Descubra nuestra línea de productos y soluciones de prueba, visibilidad y seguridad:
PRUEBE y valide el desempeño de sus soluciones de red
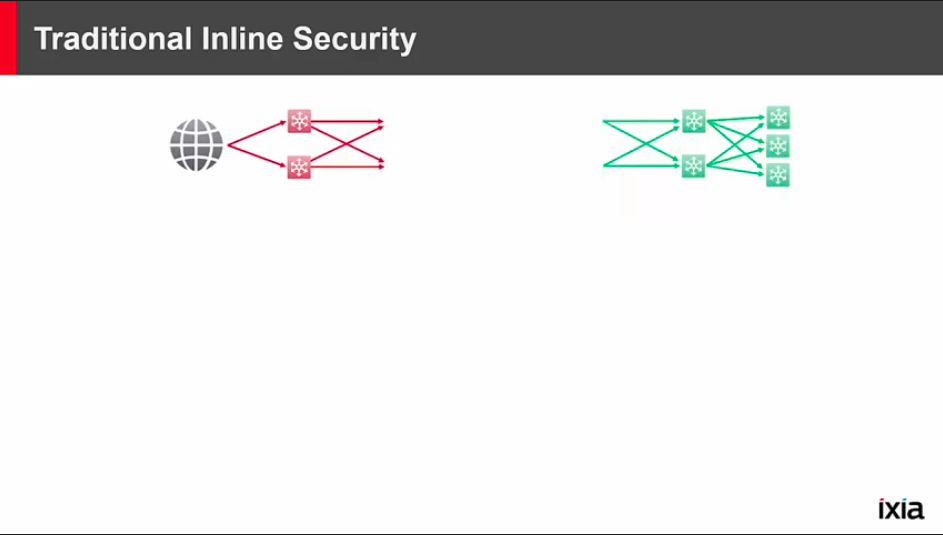
PATRULLE cada paquete con visibilidad continua; mejore la seguridad de la red y la información de monitoreo
PROTEJA a sus usuarios y aplicaciones, simule amenazas, elimine los puntos ciegos y tome el control de una superficie de ataque que cambia rápidamente
Contacto: Felix Lopez- Ingeniero de Producto
VERIFY YOUR NETWORK
Network test for higher Ethernet speeds, higher port densities, network switches and routers, and software-defined networks require many different technologies — both physical and virtual — used in a single network infrastructure. Every upgrade requires re-evaluating network-level traffic scale, application diversity, and attack surface resilience. End-users demand speed and security so there is no margin for error when deploying new network equipment.
Network equipment manufacturers must validate their equipment against the latest applications, traffic volumes, and user behavior diversity. Service providers and large enterprises must do the same. There can be no compromises in testing realism.
The directive for many IT departments is to be part of the business innovation process. How do you innovate? The average IT team spends more than half of their day just on problem resolution or network security issues.
Network visibility starts at the foundation of your network. It allows you to expose and resolve hidden problems (blind spots) faster. Faster resolution times mean more TIME to innovate the network design and the applications running on top of it.
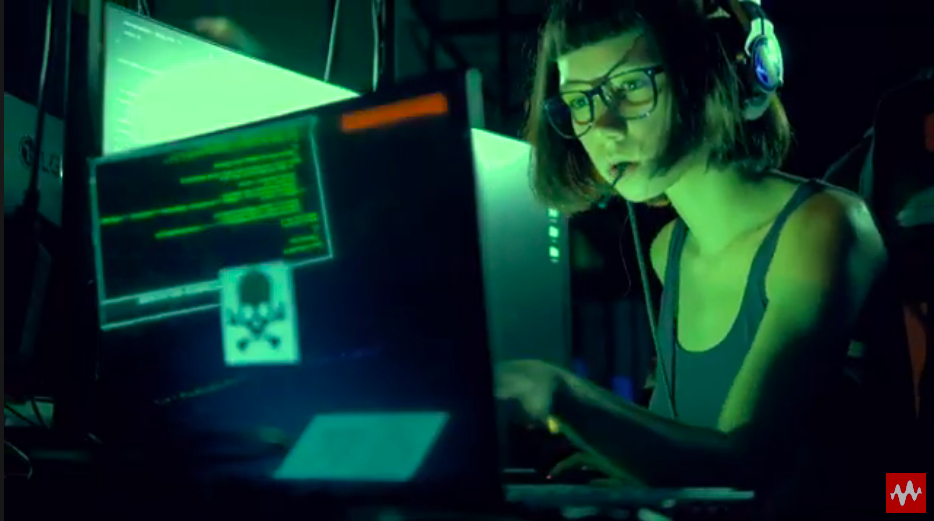
PROVE YOUR NETWORK IS SECURE
Get in front of attacks with breach and attack simulation (BAS)
Security is never static. New threats are ever present, and misconfigurations can compromise your network in an instant. You need to attack yourself — before someone else does. By safely simulating the entire kill chain on your production network, you can definitively measure your risk, expose gaps, and course-correct with step-by-step remediations.
A breach and attack simulation (BAS) platform built on 20+ years of leadership in threat intelligence and security testing, Keysight Threat Simulator makes it easy to continuously validate your defenses and optimize the effectiveness of your security operations (SecOps) team.
Videos KEYSIGHT

Domicilio Matriz
URBINA #5 PARQUE INDUSTRIAL NAUCALPAN ESTADO DE MEXICO C.P. 53489
55 5387 3500
contacto@maps.com.mx
Derechos de autor © Todos los derechos reservados. MAYORISTAS DE PARTES Y SERVICIOS S.A. DE C.V.